Spam viruses pose a significant risk to individuals and organizations alike. These malicious programs spread rapidly through systems, exploiting sensitive information. Spam viruses commonly camouflage as legitimate emails, tricking unsuspecting victims into activating malicious attachments. This can cause a range of devastating consequences, including data theft, system failure, and financial damage.
- Staying informed about the latest spam virus threats is crucial for effective protection.
- Deploying robust security measures, such as firewalls and antivirus software, can reduce the risk of infection.
- Demonstrating caution when opening emails from unknown senders or clicking on suspicious links is essential.
Sneaky Spread of Malware
Spam isn't just an annoyance; it's often a Trojan horse for malware. Cybercriminals are increasingly embedding malicious code into seemingly harmless emails and messages. These messages can trick you into clicking on attachments, unwittingly unleashing access to your system for ransomware. Be vigilant about suspicious emails and always double-check before interacting.
- Stay clear of opening emails from unknown senders.
- Pause your cursor over links to see the actual URL before clicking.
- Employ a reputable antivirus program and keep it updated.
Remember, prevention is key to staying safe from the stealthy spread of malware through spam.
Bug vs. Spam: A Devastating Duo
In the digital realm, a sinister duo wreaks havoc on unsuspecting users: viruses and spam. These malicious forces work in tandem to destroy systems and steal critical information. Viruses, like stealthy parasites, embed themselves into networks, replicating vulnerabilities to cause widespread chaos. Spam, on the other hand, bombards inboxes with deceptive messages, often attempting to scam users into revealing financial data. Together, these nefarious forces create a dangerous online environment.
Combating Back Against the Spam-Virus Onslaught
In today's digital landscape, malicious entities are persistently seeking to exploit vulnerabilities and compromise our systems. Spam emails and viruses have become increasingly complex, posing a grave threat to individuals and organizations alike. It is imperative that we fortify our defenses and utilize effective strategies to counter the impact of these cyberattacks.
One crucial step in this struggle is to stay informed of the latest vulnerabilities. By understanding common spam tactics and virus characteristics, we can more effectively recognize potential incursions.
- Furthermore, it is crucial to utilize robust security software, including antivirus programs and firewalls. These tools can provide a initial barrier against malware and unwanted traffic.
- Ensuring timely updates for operating systems, applications, and security software is paramount. Updates often include fixes for known vulnerabilities that cybercriminals could take advantage of.
- Finally, it is important to practice safe browsing habits. Be cautious about clicking on questionable connections and refraining from downloading software from untrusted sources.
By following these guidelines, individuals and organizations can significantly reduce their risk of falling victim to spam-virus attacks. Remember, a proactive approach to cybersecurity is the best defense against the ever-evolving threat landscape.
Identifying and Combating Spam Malware
Spam viruses present a serious risk to computer systems, often spreading through untrustworthy websites. These threats can harm your system performance, leading to data breaches. To safely mitigate spam viruses, it's crucial to implement a multi-layered defense strategy. This includes installing reliable security programs, keeping your software current, and exercising vigilance with email attachments. Always keep in mind that education and awareness are key to staying protected from these ever-evolving threats.
Spam's Transformation: Annoyance to Menace
What website began as a minor irritation, spam has transformed into a serious threat. Early spam was primarily advertisements flooding inboxes. While irritating, it was mostly benign. Today's spam, however, is far more malicious.
Cybercriminals now utilize spam to spread viruses and steal sensitive data. They use deceptive methods to trick users into clicking on suspicious files. This can lead to identity theft, financial loss, and even security vulnerabilities.
- Furthermore|In addition|, spam continues to evolve. New techniques emerge constantly, making it a relentless foe. Users must remain vigilant and implement safeguards to minimize their risk.
Educating oneself is crucial in the fight against spam. By understanding the evolving nature of this cyber threat, individuals can mitigate their vulnerabilities.
 Neve Campbell Then & Now!
Neve Campbell Then & Now!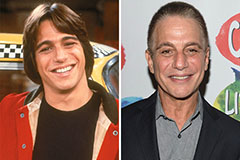 Tony Danza Then & Now!
Tony Danza Then & Now! Danica McKellar Then & Now!
Danica McKellar Then & Now! Shane West Then & Now!
Shane West Then & Now! Robbie Rist Then & Now!
Robbie Rist Then & Now!